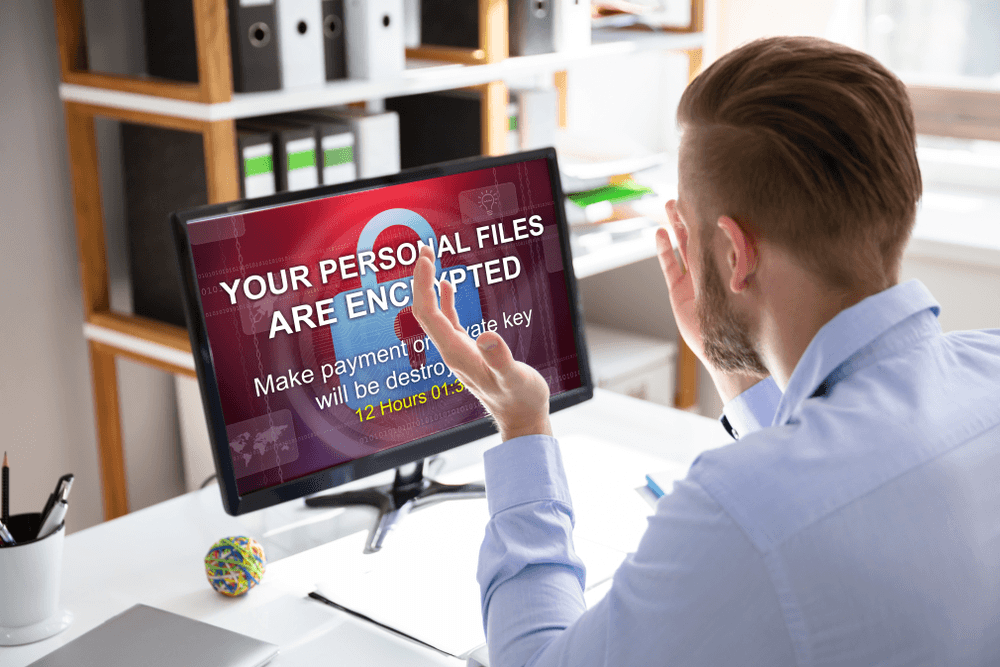
Ransomware là loại mã độc cực kỳ nguy hiểm và ko dễ dàng bị phát hiện. Đó cũng là lý do vì sao ransomware lại trở thành một chủ đề hot và luôn là mối đe dọa cho rất nhiều doanh nghiệp Việt Nam cũng như thế giới.
Ransomware được coi là một trong những mối đe dọa phần mềm độc hại lớn nhất năm 2018 và nó tiếp tục phá vỡ hoạt động của các doanh nghiệp và cuộc sống của người dùng trên toàn thế giới vào năm 2019. Các nhà nghiên cứu bảo mật đã và đang theo dõi hơn 1.100 biến thể ransomware khác nhau và con số này đã không ngừng tăng lên trong thời gian gần đây. Đủ cho thấy ransomware ngày càng tinh vi hơn và tội phạm mạng đã tích cực sáng tạo ra nhiều loại ransomware nguy hiểm hơn rất nhiều. Dưới đây là danh sách một số loại ransomware khét tiếng nhất trong những năm gần đây mà bạn nên biết để có những biện pháp phòng tránh kịp thời.
1. Bad Rabbit
Ransomware Bad Rabbit xảy ra sau các dòng mã độc WannaCry và NotPetya với quy mô rộng hơn và đã lây nhiễm các tổ chức chủ yếu ở Nga và Đông Âu. Chuyên gia bảo mật của ESET và Proofpoint nói rằng ban đầu Bad Rabbit được phát tán qua gói cập nhật Adobe Flash giả mạo nhưng ransomware cũng có công cụ riêng để di chuyển bên trong mạng lưới. Điều này cũng giải thích vì sao Bad Rabbit lại lan tràn một cách nhanh chóng trong một thời gian ngắn.
Nếu người dùng nhấp vào trình cài đặt độc hại, máy tính của họ sẽ bị khóa và nạn nhân sẽ phải trả tiền chuộc khoảng 280 đô la Bitcoin với thời hạn 40 giờ để thực hiện thanh toán.

Ransomware Bad Rabbit lan rộng nhanh chóng chỉ trong thời gian ngắn
2. Cerber
Cerber là một trong những loại ransomware tồi tệ nhất đã trở nên tồi tệ hơn. Ngoài việc mã hóa các tập tin và đòi tiền chuộc, giờ đây nó còn có thêm khả năng đánh cắp ví Bitcoin và thông tin mật khẩu người dùng.
Nhắm vào người dùng Office 365 và sử dụng chiến dịch lừa đảo công phu, Cerber đã ảnh hưởng đến hàng triệu người dùng trên toàn thế giới, ngoại trừ các quốc gia hậu Xô Viết. Nạn nhân sẽ nhận được email mang địa chỉ của Microsoft Office có chứa mã độc. Sau mở email, ransomware sẽ âm thầm phát tán và mã hóa dữ liệu trên máy tính người dùng. Khi giai đoạn mã hóa hoàn tất, Cerber sẽ để lại những thông báo đòi tiền chuộc ở dạng .TXT, .HTML và .VBS tại mỗi thư mục có chứa dữ liệu bị mã hóa. Mã độc này đòi tiền chuộc 1.24 bitcoin (khoảng 520$) và khoản tiền này tăng gấp đôi nếu như sau 1 tuần không trả tiền chuộc.
3. Gandcrab

Hacker sử dụng email spam để phát tán mã độc GandCrab
Gandcrab là một số ít các ransomware yêu cầu thanh toán bằng tiền điện tử và sử dụng tên miền cấp cao (TLD). Điều ngạc nhiên là tên miền TLD này lại không bị ICANN xử phạt, do đó đã vô tìn cấp thêm một mức độ “bảo mật” cho bọn tội phạm.
Hơn thế nữa, Gandcrab dựa nhiều vào các Macro Microsoft Office, VBScript và PowerShell để tránh bị phát hiện và sử dụng mô hình ransomware-as-a-service (RaaS) để tối ưu hóa việc phân phối trong khi hacker chỉ cần tập trung vào email spam gửi đến người dùng. Số tiền chuộc để lấy lại dữ liệu có thể dao động từ 400 USD – 1.000 USD. Sau hơn một năm thống trị các hệ thống máy tính mạng trên toàn thế giới, cuối cùng Gandcrab cũng công bố ngừng hoạt động sau khi thu về hơn 2 tỷ USD từ nạn nhân và các chuyên gia bảo mật cũng đưa ra bộ giải mã mới nhất dành cho mã độc GandCrab.
4. Katyusha
Katyusha là một trojan ransomware mã hóa được phát hiện lần đầu tiên vào tháng 10 năm 2018. Nó mã hóa các tệp thêm phần mở rộng .katyusha và yêu cầu thanh toán tiền chuộc 0.5 bitcoin trong vòng 3 ngày. Katyusha đe dọa sẽ tiết lộ dữ liệu của nạn nhân nếu tiền chuộc không được thanh toán và cũng như các bản sao lưu trước đó cũng sẽ bị ransomware này làm “bay hơi”. Hacker thường sử dụng các file đính kèm trong email để phát tán Ransomware Katyusha. Cho đến hiện tại, vẫn chưa có công cụ nào có khả năng bẻ khóa mã hóa mã độc này.
5. LockerGoga
LockerGoga là một ransomware tương đối mới, nhưng thiệt hại của nó gây ra không hề nhỏ và theo dự báo danh sách nạn nhân sẽ vẫn còn tiếp tục tăng lên theo thời gian. Điểm khác thường của mã độc này khác với các ransomware thông thường là nó sẽ buộc nạn nhân thoát khỏi thiết bị bị nhiễm, điều này thường dẫn đến việc nạn nhân không thể xem thông báo tiền chuộc và hướng dẫn về cách khôi phục tệp.
Đầu năm 2019, ransomware LockerGoga đã tấn công một số doanh nghiệp và sản xuất, gây ra những thiệt hại đáng kể. Sau khi tấn công vào Công ty tư vấn kỹ thuật Altran của Pháp, nó tiếp tục xâm nhập vào Tập đoàn Norsk Hydro - một trong những tập đoàn sản xuất nhôm và năng lượng tái tạo lớn nhất thế giới tại Na-uy và hai công ty hóa chất lớn có trụ sở tại Hoa Kỳ.
6. Ryuk
Ryuk cũng là một trong những mã độc nằm trong danh sách ransomware mới, xuất hiện lần đầu vào tháng 8 năm 2018 và từ đó đã “đút túi” hơn 3,7 triệu USD dưới dạng Bitcoin nhờ vào việc tống tiền 52 nạn nhân hớ hênh không bảo vệ cẩn thận máy chủ cũng như dữ liệu của họ. Chỉ cần nhìn vào số tiền thu được và số lượng nạn nhân cũng đủ cho thấy những kẻ đứng sau mã độc Ryuk này rất kiên nhẫn, sẵn sàng chờ đợi những con mồi béo bở có hành động bất cẩn.
Cách tấn công của Ryuk cũng không có gì mới mẻ. Những email spam được gửi đến tài khoản của doanh nghiệp. Khi lỡ tay bất cẩn click vào email đó bao gồm cả file đính kèm được tạo ra hết sức cẩn thận, các hacker cơ đã có thể chiếm quyền kiểm soát của toàn bộ hệ thống.
Tinh vi hơn, chúng còn bỏ ra cả năm trời để lựa chọn con mồi, loại bỏ những doanh nghiệp không đủ lớn để tống tiền. Điều này khiến cho những công ty bị lọt vào tầm ngắm mà vẫn không hay biết để thực thi chính sách bảo mật kịp thời.
7. SamSam
SamSam là một chủng loại ransomware được sử dụng phổ biến nhất trong các cuộc tấn công ransomware được nhắm mục tiêu. SamSam đã tấn công một loại các ngành công nghiệp Mỹ, chủ yếu là cơ sở hạ tầng quan trọng như bệnh viện, công ty chăm sóc sức khỏe. Năm ngoái, cuộc tấn công SamSam đã làm tê liệt thành phố Atlanta trong nhiều ngày và khiến người nộp thuế phải trả gần 17 triệu USD.
Không giống như các chiến dịch ransomware khác dựa trên kỹ thuật lừa đảo để phân phối, SamSam sử dụng Giao thức máy tính từ xa (RDP) để xâm nhập vào hệ thống mạng của nạn nhân. Cho đến này, khoản tiền chuộc lớn nhất được trả để giải mã ransomware SamSam của một nạn nhân có giá trị 64 nghìn USD – một số tiền đáng kể so với hầu hết các họ ransomware.
Ransomware có thể phòng ngừa

Giải pháp bảo mật ngăn chăn sự tấn công của ransomware
Như chúng ta đã thấy trong những năm gần đây, các mối đe dọa từ ransomware đang phát triển theo một cách đáng sợ. Các cuộc tấn công xuất hiện với tần suất lớn hơn, tinh vi hơn trong những phương thức tấn công ngay cả những bản sao lưu cũng không thể tồn tại khi có sự xâm nhập của ransomware.
Đây là một thực tế mà tất cả các doanh nghiệp hiện nay cần phải có biện pháp phòng tránh. Với hệ thống bảo mật email – Receive GUARD sử dụng công nghệ trí tuệ nhân tạo AI và máy học để phân tích hành vi người dùng giúp bảo vệ dữ liệu doanh nghiệp trước bất kỳ mối đe dọa nào có ý định xâm nhập, kể cả đó là malware mới, chưa được đăng ký bởi bất kỳ cơ quan bảo mật nào trên thế giới.
Nếu không muốn chi một khoản tiền lớn để lấy lại dữ liệu bị mã hóa, hãy liên hệ ngay với VNETWORK!
Tìm hiểu thêm về dịch vụ tại đây.