Trung Tâm Ứng Cứu & Bảo Mật
An Ninh Mạng hàng đầu tại
Việt Nam & Châu Á
và an toàn an ninh mạng





MoMo là một nền tảng ví điện tử cho phép người dùng thực hiện các thanh toán, giao dịch trên các thiết bị di động. Bằng việc hợp tác với hơn 90% ngân hàng tại Việt Nam cùng 10.000 thương nhân trong nước, công ty này nắm giữ hơn 80% thị phần trong lĩnh vực thanh toán kỹ thuật số. Tính đến năm 2022, ví điện tử MoMo có hơn 31 triệu người dùng sử dụng.
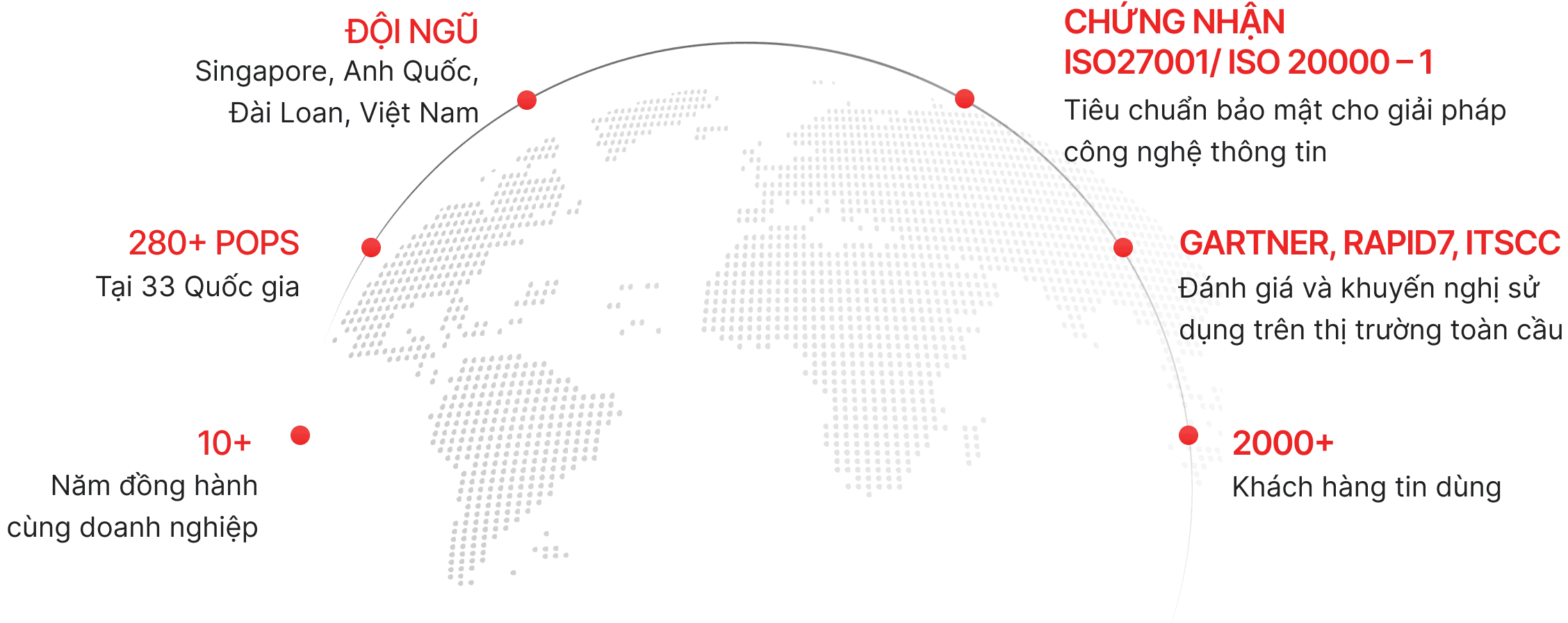
Về VNETWORK
VNIS - Bảo mật Website/App khỏi tấn công Layer 3/4/7
- Chịu tải lớn đến 2,600 Tbps với hơn 2,300+ PoPs
- Loại bỏ và ngăn chặn tấn công mạng với 2,000+ quy tắc bảo mật tiêu chuẩn OWASP top 10
- Theo dõi và xử lý sự cố mạng hiệu quả với SOC 24/7 tại Việt Nam, Singapore, Đài Loan, Hồng Kông


DDoS Protection (L3,4)
- Multi-CDN: Tăng tốc độ truy cập, giảm chi phí băng thông, bảo vệ dữ liệu
- AI Smart Load Balancing (RUM, GSLB): Tối ưu trải nghiệm website mọi lúc mọi nơi

Cloud WAF/ WAAP (L7)
- Scrubbing Center: Lọc gói tin độc hại
- Bảo vệ máy chủ gốc: Ẩn và bảo vệ IP
- Bảo mật DNS, API và Bot Management: Kiểm soát và ngăn chặn truy cập xấu
- SOC 24/7: Giám sát và nhanh chóng khắc phục mọi vấn đề kỹ thuật
EG-Platform - Bảo mật email toàn diện
- Loại bỏ các mối đe dọa từ chiều nhận, chiều gửi và spam mail với các giải pháp ReceiveGuard, SendGuard và SpamGuard
- Phát hiện và ngăn chặn các cuộc tấn công email có chủ đích với công nghệ phân tích hành vi chính xác
- Lọc sạch 99% virus mới và spam mail
- Được Gartner, ITSCC và Rapid7 chứng nhận

- Bayesian: Lọc email thông minh và hiệu quả
- Tiêu chuẩn SPF, DKIM, DMARC: Kiểm tra email spam chính xác

- AI & ML: Liên tục học và phân tích để ứng phó với các tấn công email mới nhất
- 1,000+ vùng ảo: Phân tích và cô lập mọi cuộc tấn công
- Phân tích URL: Kiểm tra URL an toàn và xác định đến tận URL cuối cùng
- Mã hóa email đáng ngờ thành hình ảnh: Phòng chống mã độc

- Bảo mật mail server: Kiểm soát toàn bộ email gửi, ngăn chặn mọi hành vi xâm nhập và lạm dụng mail server
- Giám sát hoạt động: Thông báo quản trị viên về bất kỳ hoạt động bất thường

WAAP là gì? Ưu điểm vượt trội của WAAP
Các hình thức tấn công tinh vi SQL injection, XSS và tấn công API chứa đựng tiềm ẩn rủi ro cho hệ thống thông tin của doanh nghiệp. Vì vậy, các giải pháp bảo mật dữ liệu đã và đang trở thành chủ đề được quan tâm hàng đầu hiện nay, trong đó có WAAP. Vậy WAAP là gì? Hãy cùng VNETWORK tìm hiểu.

Bare Metal Server là gì? Ưu điểm của Bare Metal Server
Bare Metal Server đang trở thành xu hướng trong lĩnh vực dịch vụ cho thuê máy chủ nhằm đáp ứng nhu cầu ngày càng tăng cao của doanh nghiệp. Vậy Bare Metal Server là gì và có những ưu điểm nổi bật nào? Hãy cùng VNETWORK tìm hiểu qua bài viết dưới đây.

Những ưu điểm khi triển khai Bare Metal Server Việt Nam
Số người sử dụng internet tại Việt Nam trong năm 2023 chiếm đến 79,1% tổng dân số. Điều này dẫn đến sự gia tăng về số lượng doanh nghiệp và các dự án công nghệ mới. Trong bối cảnh này, Bare Metal Server (BMS) đã dần trở nên phổ biến và được chấp nhận rộng rãi trong môi trường doanh nghiệp tại Việt Nam. Hãy cùng VNETWORK tìm hiểu những lợi ích khi đặt Bare Metal Server tại Việt Nam trong bài viết này.
Bắt đầu câu chuyện thành công tiếp theo
của bạn với VNETWORK ngay hôm nay
.svg)

